The Dutch Data Protection Authority (Autoriteit Persoonsgegevens) (Dutch DPA) recently published a report on personal data breaches, which provides valuable insights into the Dutch DPA’s views on incident response. It also contains some helpful statistics.
Increase in follow-up action by the Dutch DPA
It is clear from the report that the Dutch DPA is still dealing with budget and capacity constraints, forcing it to take a risk-based approach with respect to supervision. The Dutch DPA’s current approach is to focus on personal data breaches posing the greatest threat to individuals (e.g., due to the amount of affected data subjects or sensitivity of the affected data). Nevertheless, the Dutch DPA has become more active in recent years in terms of following up on notifications. Over the course of 2024, the Dutch DPA received a total of 37,839 notifications. 26,815 of these were monitored for emerging trends, 11,024 were placed under more detailed scrutiny and 28 were subjected to in-depth, formal investigations. This means that last year almost 30% of all notifications resulted in some form of follow-up by the Dutch DPA. Organisations notifying personal data breaches should therefore be prepared to answer follow-up questions from the Dutch DPA.
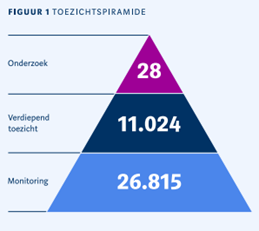
Figure 1 – oversight statistics
Ransom payments
In the report, the Dutch DPA makes clear that it is opposed to organisations paying ransoms and that doing so does not, in any way, absolve organisations of their obligations under data protection law. The Dutch DPA refers to the fact that in some instances, stolen data is still leaked or sold by ransomware threat actors even after a ransom payment is made. The Dutch DPA cautions that trusting threat actors to honour a promise, particularly regarding the deletion or non-disclosure of data, brings no certainty and can perpetuate criminal business models. This is not an especially surprising stance for the Dutch DPA to take, though it arguably disregards the significant challenges that organisations encounter when faced with ransomware attacks. When an organisation is targeted, it may find itself unable to operate, with critical systems locked and business activities brought to a standstill or very sensitive personal data compromised.
In such high-pressure situations, the guidance to simply refuse payment does not always align with the practical reality of what can ultimately be an existential event for a victim organisation. Many organisations need to balance the financial and ethical cost of paying a ransom with the stark reality that doing so may be the only way to save their business. The pressure to restore operations, protect sensitive data and minimise harm can leave them with little room to manoeuvre.
If an organisation is considering making a ransom payment, it is vital to obtain legal advice to ensure that making a payment would not be in breach of relevant sanctions laws or otherwise attract liability. At a time where ransomware groups are increasingly unstable, it is particularly important that these checks are informed by forensic analysis, ensuring that the organisation has determined the identity of the threat actor based on the tools, tactics and procedures as well as indicators of compromise. Ransom payments should not be facilitated without the input of legal advisors, digital forensic experts, threat negotiators and, wherever possible, law enforcement.
Notifying individuals
The report also highlights the Dutch DPA’s aggressive approach with respect to notifying individuals under Article 34 of the GDPR, required where an incident is likely to result in a ‘high’ risk to the rights and freedoms of an individual. Despite scrutiny over earlier public statements made by the Dutch DPA regarding the notification thresholds and clear guidance issued by the European Data Protection Board, the Dutch DPA still considers most breaches involving non-sensitive personal data (e.g., consisting only of business contact details and names) to be sufficient to constitute a high risk, meaning that notifications to individuals would be required in such cases. This is a concerning development. Applying a relatively low notification threshold may lead to notification fatigue amongst the public, potentially diminishing the effectiveness of such notifications when truly sensitive data is compromised. This interpretation of the GDPR also diverges from that of most other EU DPAs, meaning organisations wishing to take a consistent approach to multi-jurisdictional notifications will either need to notify across the continent adopting the Dutch DPA’s low threshold, or adopt the higher threshold accepted by other DPAs which would of course risk the scrutiny of the Dutch DPA.
Dutch DPA’s advisory approach
In keeping with its overarching goal of ensuring strong data protection across all sectors, the Dutch DPA does make clear that its default position is not retributive. It emphasises the importance of collaboration with, and guidance for, organisations that have experienced a data breach. By adopting a more advisory stance, the Dutch DPA claims that it can ensure that impacted organisations learn how best to inform affected individuals, take the correct remedial measures and bolster technical safeguards. As such, the risk of immediate enforcement action from the Dutch DPA following a data breach appears to be limited.
Conclusion
In our view, the report highlights a few important practical considerations for organisations:
- Robust security measures: proactive prevention remains paramount. Organisations should prioritise the implementation of comprehensive and effective security controls to mitigate the risk of data breaches.
- Documentation and incident response: following an incident, thorough investigation into the root cause is indispensable. Having an up-to-date incident response plan embedded into day-to-day operations, helps meet the regulatory expectation that organisations track, assess, and remediate breaches promptly.
- Ransomware preparedness: the Dutch DPA’s clear position that ransom payment offers no firm guarantee of data being wiped highlights the importance of engaging experienced advisors when deciding whether to engage with the threat actor and paying a ransom. Such expertise is vital both in assessing the credibility of threat actors and in ensuring compliance with sanctions regulations.
- Engagement with the Dutch DPA: with the Dutch DPA demonstrating increased responsiveness to breach notifications, it is crucial for organisations to provide early and honest notification to the Dutch DPA. While the Dutch DPA has indicated a preference for supporting compliance over immediate enforcement, it remains advisable that all notifications are carefully prepared to ensure accuracy and completeness.
If you have questions on incident response, or if you need guidance on proactive prevention, please do not hesitate to contact our team for further advice.



